Broken Validation of Whatsapp for iOS – Using / Cloning other Whatsapp Number (Jan 16th, 2015)
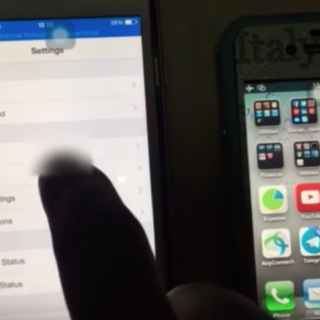
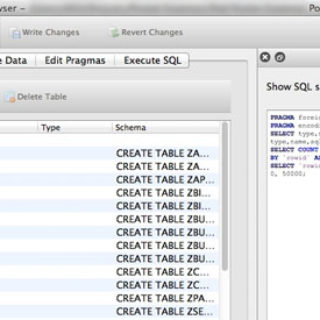
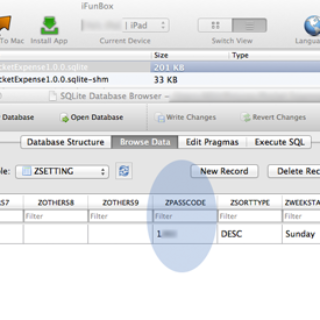
In the name of Allah, the Most Gracious, the Most Merciful. Description: In short, by copying all of the application sandbox of the active/original whatsapp account...