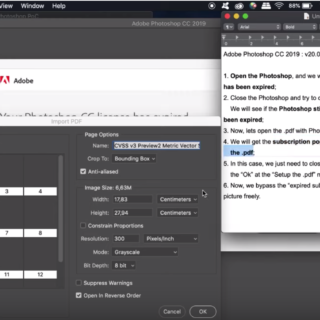
Adobe Photoshop CC 2019 v. 20.0.0 (for OS X) Expired Subscription Bypass – Bypass Trial Expired
In the name of Allah, the Most Gracious, the Most Merciful. Description: The expired subscription pop-up could be bypassed by opening the .pdf document at the...