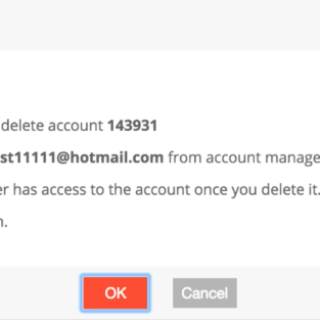
FortiNet – Unrestricted Deletion to All Other Sub Account via IDOR at Support Portal
In the name of Allah, the Most Gracious, the Most Merciful. Please kindly visit this simple paper directly to looking this release in simple:[English Version] FortiNet...