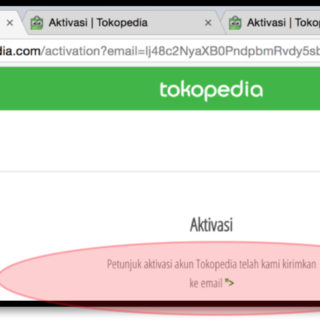
Tokopedia – Converting Content Injection to Reflected Cross Site Scripting via Base64 Encoding
In the name of Allah, the Most Gracious, the Most Merciful. I. ABSTRACT Provision of information for activating a new-registered account is one of the features...